Have you ever wanted to browse the web without revealing your identity? Or maybe you’re trying to access region-locked content, improve security, or manage multiple online accounts. If so, proxies might be the solution you need.
Then, you might find yourself wondering “What is proxy?” and “How does it work?” This guide will walk you through everything you need to know, from different types of proxies to their benefits and potential risks. By the end, you’ll have a clear understanding of how proxies can enhance your online experience.
What Is Proxy?
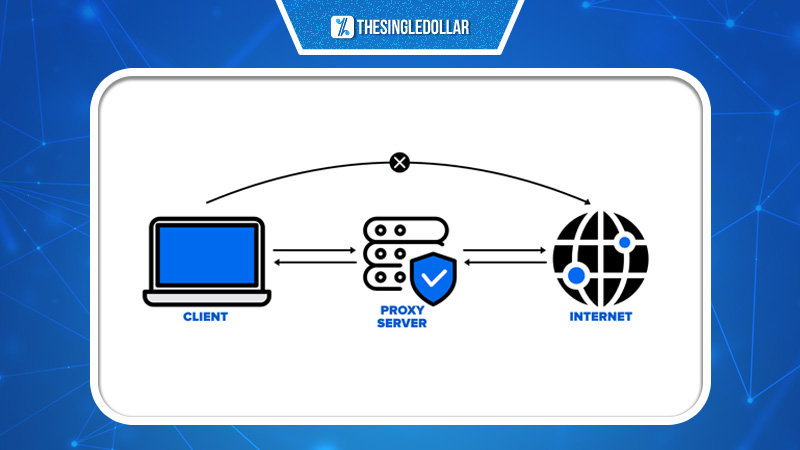
A proxy, in short, acts as a bridge between you and the internet. It serves as an intermediary that separates end users from the websites they visit, adding layers of security, privacy, and functionality based on specific needs or policies.
When you use a proxy, your internet traffic flows through it before reaching the requested website. The proxy then forwards the response back to you. In many cases, this helps mask your identity, secure data transfers, and even improve performance.
Proxies serve various purposes, from enhancing privacy to bypassing content restrictions. They’re widely used by individuals and businesses, with multiple providers offering proxy services tailored to different needs.
Types of Proxies
While all proxies function as an alternative point of access to the internet, they come in different forms, each designed for specific use cases. Knowing the differences can help you choose the right one based on your requirements.
Residential Proxy
Residential proxies assign users real IP addresses linked to physical devices, making them appear as regular home users.
They’re commonly used for ad verification, brand protection, and accessing geo-restricted content. While highly reliable, they tend to be more expensive compared to other proxy types.
Datacenter Proxy
Datacenter proxies originate from third-party data centers rather than internet service providers (ISPs). They offer fast and cost-effective solutions for web scraping and data gathering.
They’re great for speed and efficiency but lack the authenticity of residential IPs, making them easier to detect and block by websites.
Forward Proxy
A forward proxy acts as a gateway for users within an internal network, controlling outbound requests. When a request is sent, the proxy assesses whether it should allow or block the connection.
Best suited for organizations, forward proxies enhance security by hiding internal IP addresses and enabling centralized access control. However, they may limit flexibility for individual users within the network.
Anonymous Proxy
An anonymous proxy conceals your identity by masking your IP address, preventing websites from tracking your online activities.
This is ideal for users who prioritize privacy, such as employees who don’t want browsing activity linked to their organization. However, free anonymous proxies can sometimes be traps designed to collect user data, so caution is advised.
Transparent Proxy
A transparent proxy functions without altering the user experience. It can be applied discreetly, meaning users may not even realize they’re using one.
These proxies are often implemented by companies to enforce web filtering policies or improve caching. However, they’re more vulnerable to certain security threats, such as denial-of-service (DoS) attacks.
Rotating Proxy
Rotating proxies assign a new IP address for every connection request, ensuring anonymity and reducing detection risks.
These are highly effective for large-scale data collection and web scraping. However, some services offering rotating proxies use shared or public IPs, which may compromise security.

Distorting Proxy
A distorting proxy identifies itself as a proxy but manipulates its own IP address to appear as if the user is browsing from a different location.
This type of proxy is useful for accessing geo-restricted content. However, some websites automatically block distorting proxies, limiting access to certain services.
Public Proxy
A public proxy is a free proxy server accessible to anyone. It hides users’ IP addresses while they browse.
While cost-effective, public proxies are often slow due to heavy traffic and pose security risks, as they may expose user data to cyber threats.
Shared Proxy
Shared proxies are used by multiple users simultaneously, providing cost-effective access to proxy services.
They’re affordable but can result in slower speeds and potential blacklisting if other users engage in suspicious activities.
SSL Proxy
SSL proxies use encryption to secure data exchanges between clients and servers, making them ideal for privacy-conscious users.
These proxies enhance security and may improve search engine rankings for websites using SSL. However, SSL encryption can slow down performance due to its processing demands.
Reverse Proxy
Unlike a forward proxy, which serves users, a reverse proxy sits in front of web servers, handling inbound traffic and distributing it efficiently.
Reverse proxies improve website performance, load balancing, and security. However, if compromised, they can expose critical server infrastructure.
CGI Proxy
A CGI proxy allows users to browse anonymously by fetching web pages through an interface.
Although useful for bypassing restrictions, CGI proxies can generate excessive server load, leading to website slowdowns or security concerns.
How Does a Proxy Work?
Since we have already answered the question “What is proxy?”, you might continue to wonder “How does a proxy work?” Well, you need to know first that every device connected to the internet has a unique IP address, similar to a home address for receiving mail. A proxy server acts as a middleman with its own IP address, forwarding requests on behalf of users.
When you visit a website through a proxy, your request is sent to the proxy server first. It then forwards the request, retrieves the data, and sends it back to you. Along the way, it can modify or encrypt data, hide your real IP, and even block access to certain sites based on configured rules.
Pros and Cons of Using Proxies
Before choosing to use proxies, you should learn about their pros and cons.
Pros
- Security: Proxies add an extra layer of security by shielding users from direct exposure to malicious sites or cyber threats.
- Bandwidth Savings: By caching frequently visited web pages, proxies reduce bandwidth usage and improve browsing speeds.
- Performance Boost: Cached content speeds upload times for repeated requests.
- Content Filtering: Proxies help organizations restrict access to certain websites based on rules.
- Access Control: Proxies can bypass geographical restrictions, granting users access to region-locked content.

Cons
- Security Risks: Free proxies often lack encryption, making them potential data security threats.
- Browsing Logs: Some proxies may log user activity, posing privacy concerns.
- No Encryption: Without proper encryption, personal data such as usernames and passwords can be exposed.
- Slower Speeds: Public or shared proxies may lead to reduced browsing speeds due to high traffic.
FAQs
Some commonly asked questions and their answers for you
What Is Proxy?
A proxy, in short, acts as a middleman between you and the internet, separating users from the websites on the Internet, giving them more security and privacy.
What Are the Types of Proxies?
Proxies are divided into many categories, but the most notable ones are residential proxies, datacenter proxies, and rotating proxies.
What Are the Pros and Cons of Proxies?
Proxies provide you with extra security and privacy, but they don’t have encryption like VPNs, and they may make your speed slower.
Conclusion
Now that you have a solid understanding to that question “What is proxy?” and many of its usages and benefits. Now, you can decide which type best suits your needs. Whether you’re looking for privacy, security, or access to restricted content, proxies offer a flexible solution. However, choosing the right proxy service is crucial to avoid risks and maximize benefits.
If you found this guide helpful, be sure to check out our other blogs at thesingledollar.com for more insights on online security and browsing tools. Have questions or experiences with proxies? Share your thoughts in the comments below!


